Malware authors continue to trick users abusing legitimate services, one recent example of this is the new campaign of Raccoon information-stealing malware.
The Raccoon Stealer Malware is written in C++ by Russian-speaking developers and it developed to compromise both 32 and 64-bit operating systems.
It was sold on underground forums in both Russian and English as a malware-as-a-service model with active chat support and GUI interface.
Bypassing Email Security Gateways
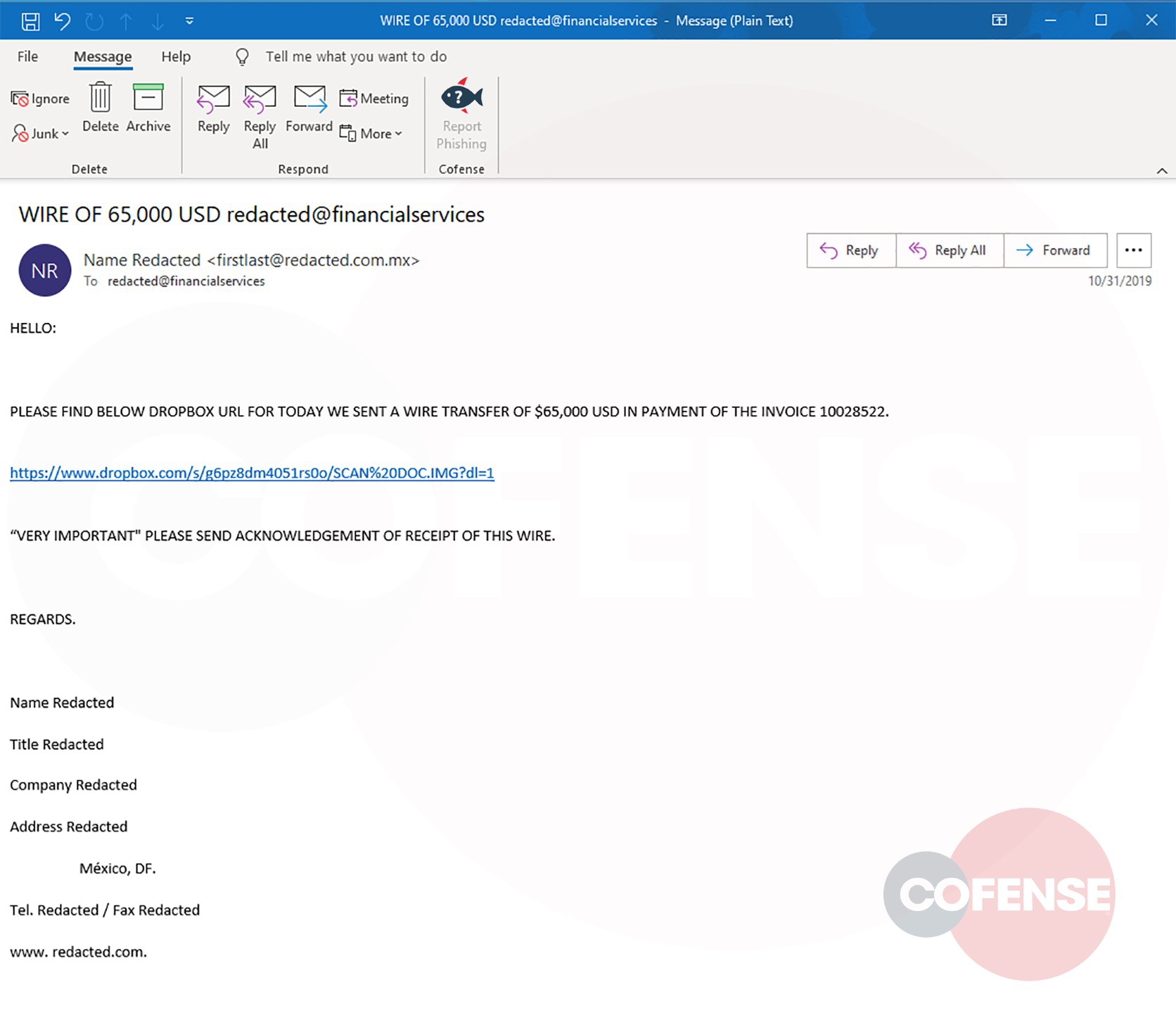
With the current campaign the threat actors hosting the malicious payload on a Dropbox share and delivered through email targeting financial organization.
The Raccoon Stealer delivered by direct attachments and via RTF documents leveraging Remote Code Execution Vulnerability CVE-2017-8570.
According to Cofense analysis, “with the current campaign, a potentially compromised email account was used to send the email shown, which managed to make its way past Symantec Email Security and Microsoft EOP gateways without the URL being removed or tampered.”
The raccoon is a new malware that emerges on underground markets since April 2019. The malware is known for quickly gathering information and to exfiltrate the data to the C&C server. Also, it is capable of downloading additional payloads.
Once the malware gets executed it connects with the C2 server that includes “bot ID” and “configuration ID”. The C2 server responds with JSON object including C2 data, payload location, and other additional files.
Researchers believe that Raccoon malware in the future with additional developments can be used as a loader malware for generating additional income.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
