Hackers abuse legitimate RDP service to use fileless attack techniques for dropping multi-purpose off-the-shelf tools for device fingerprinting and to deploy malicious payloads ranging from ransomware to cryptocurrency miners.
The Remote Desktop is the built-in feature with most of the Windows installation and it has built-in file-sharing functionality that is used by the attackers as an infection vector.
Abusing Remote Desktop Server Feature
The infection starts by abusing the feature of the Windows Remote Desktop Server in which the RDP client shares the virtual network file share location named “tsclient” of the connected computer. Attackers use these paths to create multiple-letter directory names.

According to Bitdefender researchers report, the attackers placed a malicious component of the attack named worker.exe located on the network share on the “tsclient” network location and it can be executed using explorer.exe or cmd.exe.
The worker.exe component provides an array of commands that includes collecting system information, architecture, CPU model and core count, RAM size, Windows version, taking screenshots, collecting the victim’s IP address and domain name, upload and download speeds, pulling information about default browsers and specific open ports.
The final command includes anti-forensic and detection-evasion purposes, which allows attackers to create Run dialog’s history.

Deploying Malicious Payload
By gathering details about the infected machine allows attackers to decide the type of malicious payload to infect the targeted. If it is an enterprise network attackers may decide to deploy ransomware.
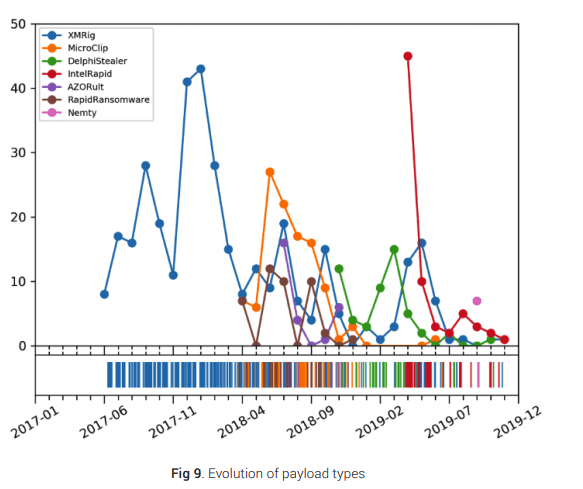
The attackers use an array of payloads starting that include Clipboard stealer payloads, Attributing off the shelf tools, Cryptocurrency stealer, Ransomware payloads, Miner payloads, and AZORult payloads.
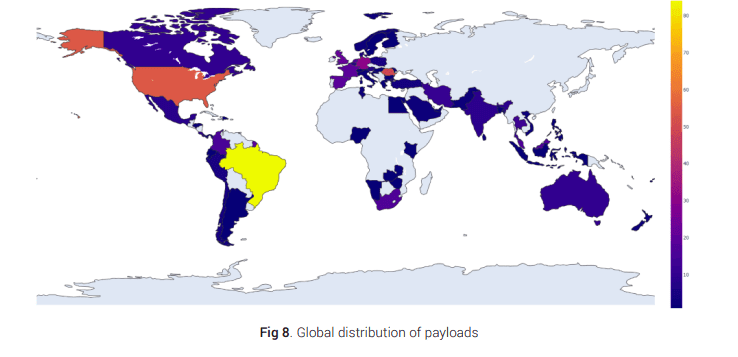
The campaign targets the victim’s around the globe, most of the victims in Brazil, the United States, and Romania. the campaign not targeted to any specific industries, it tries to infect possible victims.
Researchers further distinguish the attack type “miners were used before approximately April 2018, but since then a wide variety of tools were employed, especially until the early months of 2019.”
These types of attacks can be thwarted by disabling drive redirection from the list of group policies “Computer Configuration > Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Session Host > Device and Resource Redirection.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates



.png
)
