Researchers discovered a severe vulnerability in Amazon’s Ring Video Doorbell let hackers intercept the WiFi network credentials and bypass the home security.
By Connecting Amazon’s Ring doorbell with Alexa then by enabling announcements to be alerted when your doorbell is pressed or motion is detected.
Amazon’s Ring Doorbell uses a local WiFi network to connect to the internet and the services managed through the vendor cloud services.
If the internet single is low, then it halts the service but the ringing feature is still working, users can hear that who is behind the door.
There are multiple API endpoints( es.ring. com or ps.ring.com ) used by Ring Video Doorbell and it only communicates via the company’s cloud services.
Leaks WiFi Credentials
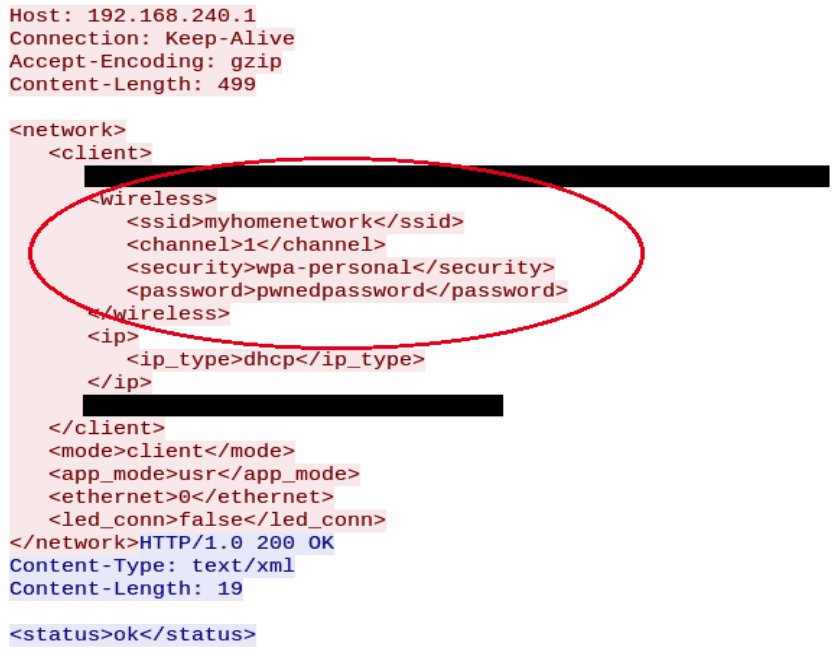
A Wireless connection used in the device to join with a local area network and the smartphone app required to send wireless network credentials to the device during the initial configuration.
In this case, “This takes place in an unsecured manner, through an unprotected access point. When entering configuration mode, the device creates an access point without a password (the SSID contains the last three bytes from the MAC address)” Bitdefender said.
All the communication including the app sends the credentials to the local network via an unprotected HTTP request, it allows attackers to clearly eavesdrop the network communication.
Deauthentication messages
“Since the credentials of the local wireless network are sent through an unsecured local network This can be exploited by a nearby attacker to obtain the user’s network credentials.”
In order to trick victims, the attacker continuously sending the de-authentication messages, which leads the device to drop from the network.

“Deauthentication is the process that allows a third party to mount the attack. It must be performed until the owner notices that the device misbehaves. This might take a while, because the doorbell will still ring the chime when the button is pressed. The only difference is that it will not send a notification and cannot be reached by the remote servers”
When the user clicks the button called “Live View” in the app, it suggests rebooting the router or presses the setup button twice on the doorbell.
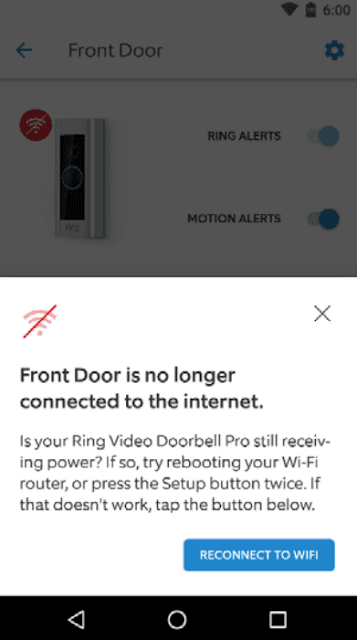
If the user presses the button then the device tries to reconnect the network, Meanwhile, the attacker is sniffing all the packets where he could find the plaintext credentials.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates



