According to a joint Cybersecurity Advisory (CSA) from the FBI, CISA, and MS-ISAC published in September 2022, Vice Society actors have recently been primarily targeting the education sector with ransomware assaults.
As the 2022–23 school gets started and malicious ransomware groups see prospects for successful operations, the CSA continued to predict an increase in attacks.
Vice Society Ransomware Gang Targeting Schools
Vice Society is notorious for targeting the education sector – K-12 and higher education institutions in particular (as referenced in the recent CISA Advisory).
Experts say ‘Vice Society’ is known for using forks of pre-existing ransomware families in their attack chain that are offered for sale on DarkWeb marketplaces.
Initially, it was noted that their attack chain included an exploit for the CVE-2021-34527 (also known as PrintNightmare) vulnerability.
“The gang is also known to target backups and exfiltrate data from compromised systems to be leveraged for the purpose of double extortion, a common ransomware operation tactic where victims are pressured to pay a specified ransom amount in exchange for decryption and to avoid having sensitive data published on the attacker’s dedicated leak site”, reports Palo Alto Networks.
Vice Society Employed Numerous Distinct Ransomware Strains
- Vice Society infected victims with the HelloKitty virus in June 2021.
- Vice Society employed Zeppelin to attack Windows hosts in 2021 and 2022.
- These attackers used vulnerabilities like PrintNightmare during their 2021 attacks to escalate privileges and expand laterally across targeted networks.
Since educational institutions are the group’s main target, this can be a sign that they’re coordinating their activities with this industry’s particular calendar year. Other targeted sectors include healthcare and nongovernmental organizations (NGOs).
Researchers say the overall attack surface expanded since many organizations use outdated hardware that hasn’t been patched against the most recent vulnerabilities as a result of a lack of spending for systems and security solutions.
Further, controlling and managing the numerous personal devices that students and staff members bring into these organizations is another issue. Due to the possibility of them interacting with personal files via cloud services, these personal gadgets carry an inherent risk.
“Although these sectors might have dedicated IT or security teams that run traditional security solutions such as an intrusion detection system (IDS) or intrusion prevention system (IPS), ransomware threat actors are leveraging living off the land techniques that can effectively circumvent traditional signature-based detection mechanisms”, researchers
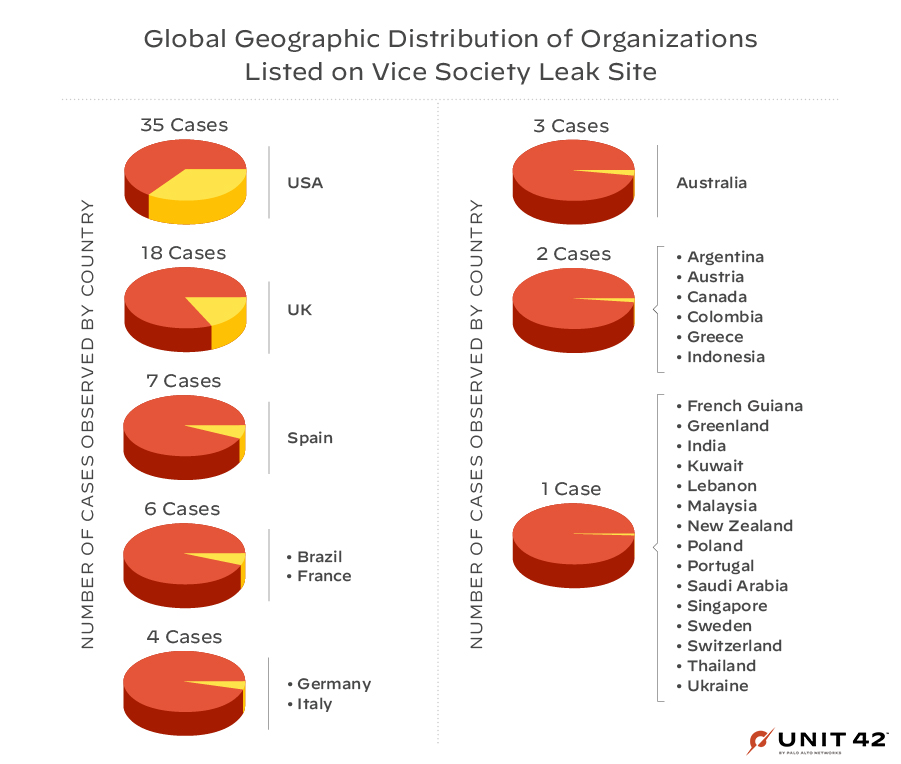
The majority of the group’s victims are organizations in the United States, United Kingdom, Spain, France, Brazil, Germany, and Italy.
Vice Society appears to have had the greatest influence on educational institutions this year, according to data from leak sites, with at least 33 educational institutions identified on the group’s dedicated ransomware leak site.
Vice Society’s observations on Ransom Demands
- Initial demands by this actor could exceed $1 million.
- Final demands after negotiations were as high as $460,000.
- The difference between initial demands and final demands could be significant. It decreases by as large as 60%.
Implement Security Best Practices
The reports say school districts with low resources and cybersecurity expertise are frequently the ones most at risk from threat actors.
Further, schools with strong cybersecurity programs may be at risk due to the opportunistic targeting frequently observed with cyber criminals. Due to the volume of sensitive student data that is accessible through school systems or its managed service providers, K-12 institutions may be considered as particularly profitable targets.
Therefore, it is recommended that educational institutions should keep up the implementation of security best practices and be alert to the continuous ransomware threat, particularly at the beginning and end of the school year.
Penetration Testing As a Service – Download Red Team & Blue Team Workspace



.png
)
