Waterbug APT Hackers used hijacked infrastructure to attack governments and international organizations through various campaigns using new and publically available malware. The group also use living off the land for executing process on the systems.
Symantec observed the targeted attack over the past year using unique tools and the campaigns hitting Europe, Latin America, and South Asia.
Multiple Campaigns
Symantec observed multiple campaigns using different toolsets on the attack campaigns, including custom malware.
The first campaign uses new malware dubbed Neptun, to target exchange servers. The Neptun malware installed on exchange servers and get commands from attackers passively. It is capable of downloading additional tools, upload stolen files, and execute shell commands.
The second campaign uses the publically available Meterpreter backdoor along with the two custom loaders, custom backdoor, and a custom Remote Procedure Call. It appears the hacker group uses Meterpreter since 2018.
The third campaign employees a new RPC backdoor that uses publicly available PowerShellRunner to run the PowerShell scripts to avoid detection.
Hacking Tools and Exploits used.
- A custom tool that combines EternalBlue, EternalRomance, DoublePulsar, SMBTouch
- Custom dropper malware Neptun
- Visual Basic & PowerShell scripts
- Publicly available tools such as RPC commands, SScan, NBTScan for scanning network
- PsExec for lateral movement, Mimikatz for stealing credentials and Certutil.exe to decode remote files.
Symantec lists the governments and international organizations attacked by Waterbug that includes governments, international organizations, IT, and education sectors across the globe.
“Waterbug’s use of Crambus infrastructure appears to have been a hostile takeover, during the attack campaigns customized variant of Mimikatz was downloaded Crambus-controlled network infrastructure.”
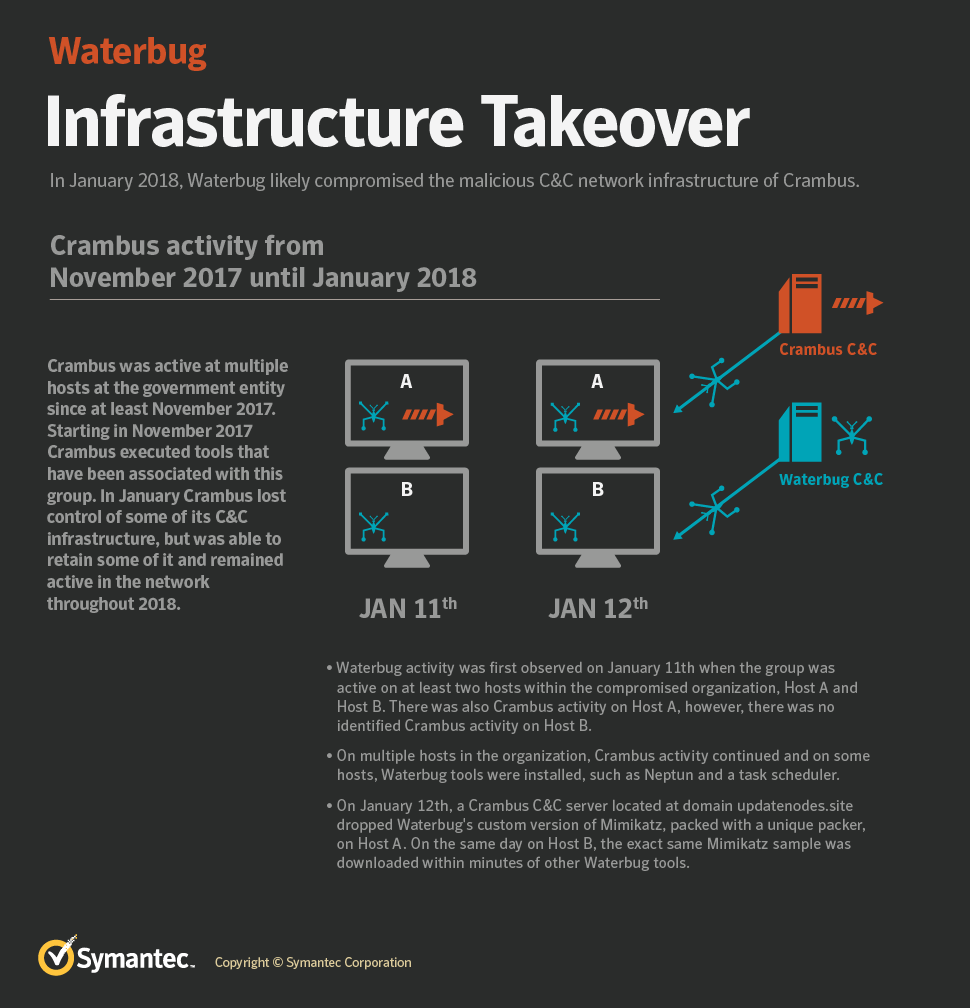
Another tool IntelliAdmin also detected on the victim’s network, which was previously used by Crambus gives more closure resemble that Waterbug group compromise the Crambus infrastructure.
“Waterbug’s frequent retooling ability demonstrates a high degree of adaptability by a group determined to avoid detection by staying one step ahead of its targets.”
Indicators of Compromise of all the three campaigns can be found here.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity courses online to keep yourself updated.
Related Read
Iranian Based OilRig APT Hackers Owned Email Hacking Tool Leaked in Telegram



.png
)
