A new malware dubbed “Messagetap” designed to monitor and record SMS traffic of certain phone numbers, IMSI numbers, and based on keywords for subsequent theft.
The new malware was developed by the Chinese APT41 hacker group to deploy in the telecommunications network. The malware was discovered by FireEye during an investigation at a telecommunications network provider.
APT41 is the Chinese state-sponsored hacker group, know for conducting financially motivated operations, the group found to be active at least from 2012.
The Messagetap malware found in a cluster of Linux servers that used for as Short Message Service Center (SMSC) servers. In the telecommunication network, SMSCs operate to store, forward, convert and deliver Short Message Service.
Messagetap Malware
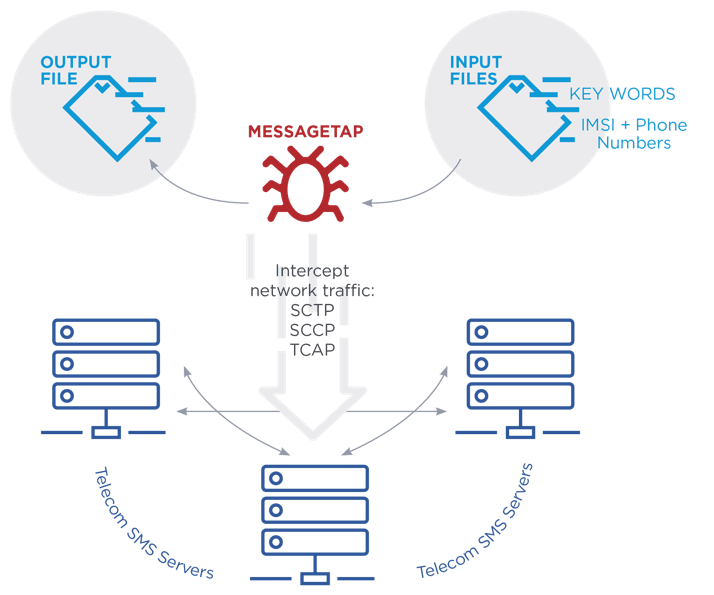
Once this malware get’s installed in a Linux SMSCs, they check for the existence of two files named keyword_parm.txt and parm.txt. These files contain for Messagetap malware.
parm.txt – File contains IMSI numbers and phone numbers to target.
keyword_parm.txt – Contains Keyword list that is read into keywordVec
The configuration files provide the target for malware, keyword_parm.txt contains keywords of geopolitical interest and parm.txt contains two list phoneMap(phone numbers) and imsiMap(IMSI numbers).
The malware installation script tries to read configuration files for every 30 seconds if the configuration files exist they are loaded into memory and files will get deleted.
“Messagetap begins monitoring all network connections to and from the server. It uses the libpcap library to listen to all traffic and parses network protocols starting with Ethernet and IP layers. It continues parsing protocol layers including SCTP, SCCP, and TCAP,” reads FireEye report.
The malware extracts the following data from the network
- SMS message contents
- The IMSI number
- The source and destination phone numbers
“The malware searches the SMS message contents for keywords from the keywordVec list, compares the IMSI number with numbers from the imsiMap list, and checks the extracted phone numbers with the numbers in the phoneMap list.”
If the SMS message matches the phone number, IMSI number or keywords they are saved to CSV file by the threat actor.
In addition to Messagetap SMS theft, FireEye also identified the threat actor interacting with call detail record (CDR) databases to query, save and steal records during this same intrusion.
The threat actor group continues to target other organizations such as travel services and healthcare providers beyond telecommunication to steal sensitive details of specific individuals.
Recently researchers discovered a new attack dubbed Simjacker, that can be exploited by sending an SMS containing a specific type of spyware code.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
