Over 170,000 users have fallen victim to a meticulously orchestrated scheme exploiting the Python software supply chain.
The Checkmarx Research team has uncovered a multi-faceted attack campaign that leverages fake Python infrastructure to distribute malware, compromising the security of countless developers and organizations.
This article delves into the attack campaign, its impact on victims, the tactics, techniques, and procedures (TTPs) employed by the threat actors, and the critical findings from Checkmarx’s investigation.
Attack Campaign Description
The core of this malicious campaign revolves around an attacker’s ability to combine several TTPs to launch a silent attack on the software supply chain, specifically targeting the Python ecosystem.
Free Webinar : Mitigating Vulnerability & 0-day Threats
Alert Fatigue that helps no one as security teams need to triage 100s of vulnerabilities.:
- The problem of vulnerability fatigue today
- Difference between CVSS-specific vulnerability vs risk-based vulnerability
- Evaluating vulnerabilities based on the business impact/risk
- Automation to reduce alert fatigue and enhance security posture significantly
AcuRisQ, which helps you to quantify risk accurately:
By creating multiple malicious open-source tools with enticing descriptions, the attackers lured victims into their trap, primarily through search engines.
The campaign’s sophistication is evident in distributing a malicious dependency hosted on a fake Python infrastructure, which was then linked to popular projects on GitHub and legitimate Python packages.
A chilling account from Mohammed Dief, a Python developer and one of the campaign’s victims, highlights the stealth and impact of the attack.
Dief encountered a suspicious error message while working on his laptop, the first sign of the compromise, leading to the realization that his system had been hacked.
Victims and Impact
Among the notable victims of this campaign is the Top.gg GitHub organization, a community boasting over 170,000 members.
The attackers managed to hijack GitHub accounts with high reputations, including that of “editor-syntax,” a maintainer with write permissions to Top.gg’s repositories.
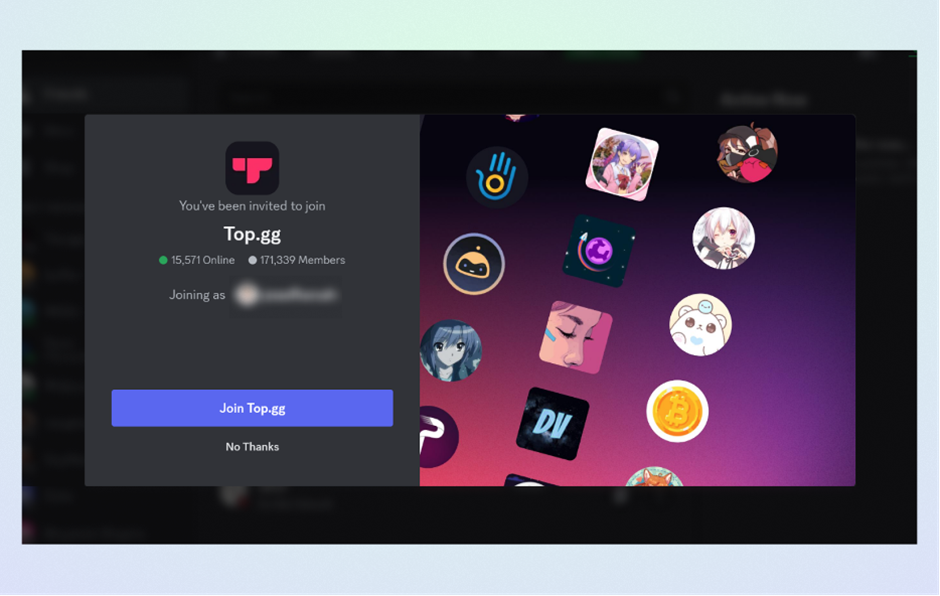
This allowed them to commit malicious acts and increase the visibility and credibility of their malicious repositories.
The attack’s impact is far-reaching, affecting individual developers and larger communities alike.
Social engineering schemes, account takeovers, and malicious packages published on the PyPi registry have underscored the software supply chain’s vulnerability to such sophisticated attacks.
The Checkmarx Research team has uncovered an attack campaign aimed at the software supply chain.
The campaign appears to have successfully exploited multiple victims.
Threat Actors and TTPs
The threat actors behind this campaign demonstrated high sophistication and planning.
They employed a range of TTPs, including:
- Account Takeover via Stolen Cookies: The attackers gained access to high-reputation GitHub accounts by stealing session cookies, bypassing the need for passwords.
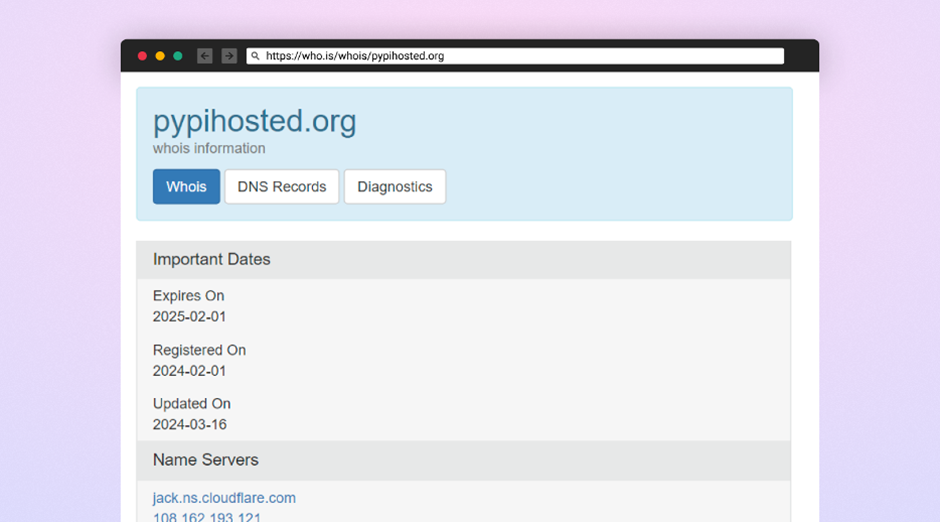
- Publishing Malicious Packages: By setting up a custom Python mirror and publishing malicious packages to the PyPi registry, they could distribute malware under the guise of legitimate software.
- Social Engineering: The attackers used social engineering to trick users into downloading malicious dependencies, further spreading the malware.
By deploying a fake Python package mirror and utilizing typosquatting techniques, the attackers could deceive users and systems into downloading poisoned versions of popular packages like “Colorama.
“The malicious payload delivered through these packages is designed to harvest sensitive information, including passwords, credentials, and data from various software applications.

The malware targets web browsers, Discord, cryptocurrency wallets, and Telegram, and even includes a keylogging component to capture victims’ keystrokes.
The final stage of the malware reveals its data-stealing capabilities, targeting not only personal and financial information but also attempting to gain unauthorized access to victims’ social media and communication platforms.
This attack campaign highlights the critical vulnerabilities within the software supply chain, particularly in open-source ecosystems like Python’s.
The sophistication and success of the attackers in exploiting these vulnerabilities underscore the need for heightened vigilance and robust security practices among developers and organizations.
Through continuous monitoring, collaboration, and information sharing, the cybersecurity community can mitigate risks and protect the integrity of open-source software.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
.png?w=696&resize=696,0&ssl=1)

