Cybersecurity experts have uncovered a series of sophisticated cyberattacks targeting poorly managed Microsoft SQL (MS-SQL) servers.
The attackers, identified as the TargetCompany ransomware group, have been deploying the Mallox ransomware in a bid to encrypt systems and extort victims.
This recent campaign draws unsettling parallels with previous attacks involving the Tor2Mine CoinMiner and BlueSky ransomware, signaling a persistent threat to digital security infrastructures.
Integrate ANY.RUN in Your Company for Effective Malware Analysis
Are you from SOC, Threat Research, or DFIR departments? If so, you can join an online community of 400,000 independent security researchers:
- Real-time Detection
- Interactive Malware Analysis
- Easy to Learn by New Security Team members
- Get detailed reports with maximum data
- Set Up Virtual Machine in Linux & all Windows OS Versions
- Interact with Malware Safely
If you want to test all these features now with completely free access to the sandbox:
The TargetCompany group’s modus operandi involves exploiting vulnerabilities in improperly managed MS-SQL servers.
By employing brute force and dictionary attacks, the attackers gain unauthorized access, primarily targeting the SA (System Administrator) account.
Once inside, they deploy the Remcos Remote Access Tool (RAT) to take control of the infected system.
As per the AhnLab Security Intelligence Center (ASEC), there has been a rise in attacks by threat actors on MS-SQL servers to deploy ransomware.
This is followed by the installation of remote screen control malware and, eventually, the Mallox ransomware.
- Remcos RAT Deployment: Utilized for initial system breach and control, facilitating further malware installation.
- Remote Screen Control Malware: Installed to enhance remote access capabilities, enabling attackers to execute subsequent phases of the attack.
- Mallox Ransomware: The final payload, designed to encrypt the victim’s files, rendering them inaccessible without a decryption key.
On-Demand Webinar to Secure the Top 3 SME Attack Vectors: Watch for Free.
Remcos RAT: A Gateway to Infection
Remcos RAT, a tool marketed for legitimate remote management, has been repurposed by attackers for malicious activities.
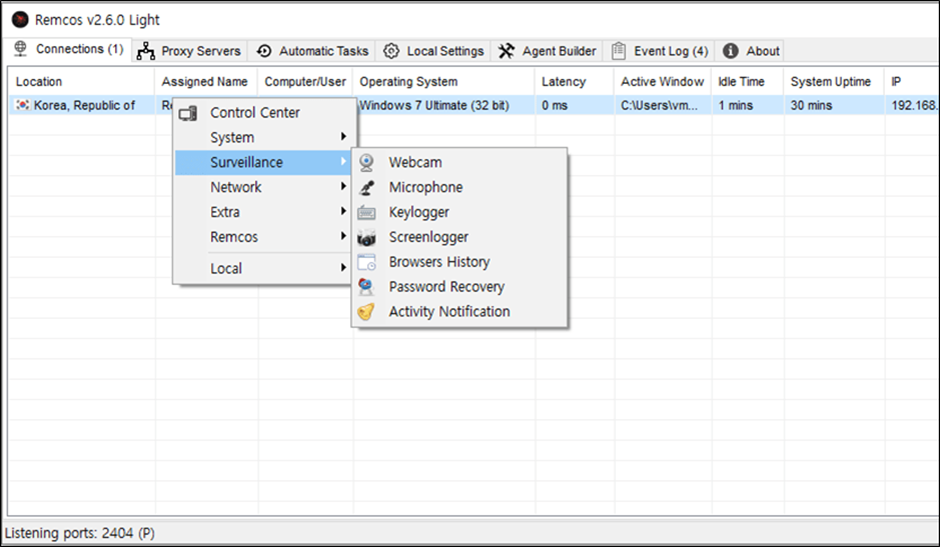
Its capabilities include keylogging, screenshot capture, and control over webcams and microphones.
In the recent attacks, a lighter version of Remcos RAT was used, indicating a strategic choice for smoother remote control without raising suspicion.

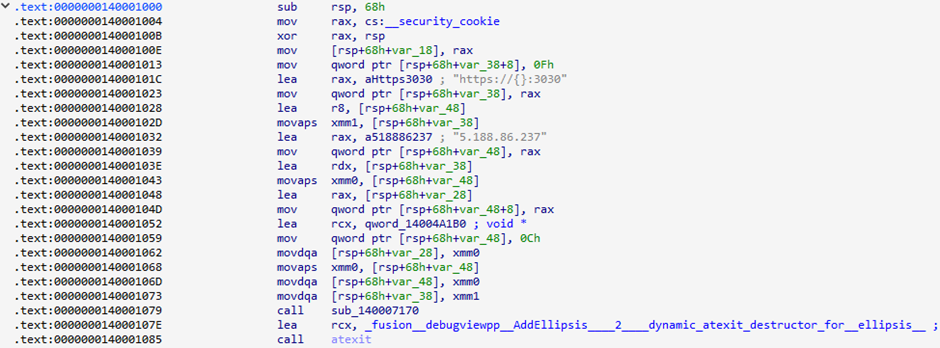
Below is the configuration data that was decrypted during the execution of Remcos RAT along with a portion of the major configurations.
| Configuration | Data |
| Host:Port:Password | 80.66.75[.]238:3388:1 |
| Assigned name | RemoteHost |
| Connect interval | 1 |
| Mutex | Rmc-8P1R4F |
| Keylog flag | Disabled |
| Keylog path | Application path |
| Keylog file | logs.dat |
| Screenshot flag | Disabled |
| Screenshot time | 10 |
| Screenshot path | AppData |
| Screenshot file | Screenshots |
| Audio record time | 5 |
| Audio folder | MicRecords |
| Copy folder | Remcos |
| Keylog folder | remcos |
Remote Screen Control Malware
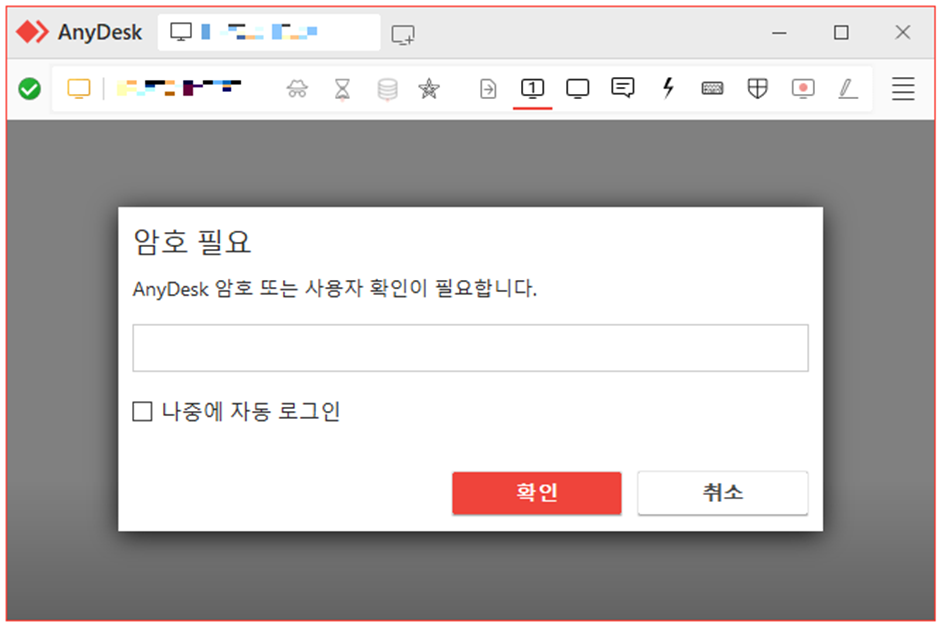
Following the initial infection, attackers deployed custom-made remote screen control malware.
To get a string, this malware first links to a C&C server’s “creds” address. However, a link to the command and control website could not be made at the time of analysis.
It is thought that the malware was able to download a string in the “ID; PW” format.
After that, this string is used to add a user account and make it part of the supervisor group.
| URL | Description |
| https://{C&C Server}/creds | Downloads user account string to be added (ID;PW format) |
| https://{C&C Server}/secret | Downloads password string to be specified when installing AnyDesk |
| https://{C&C Server}/desk | Downloads the AnyDesk installer (MSI) |
| https://{C&C Server}/gate/{AnyDesk_ID} | Sends the ID for the installed AnyDesk instance |
The threat players could get into the infected system using the AnyDesk ID they got from the command and control server.
They could then verify their identity using the password sent through “secret” and take control of the infected system.
Mallox Ransomware: The Final Blow
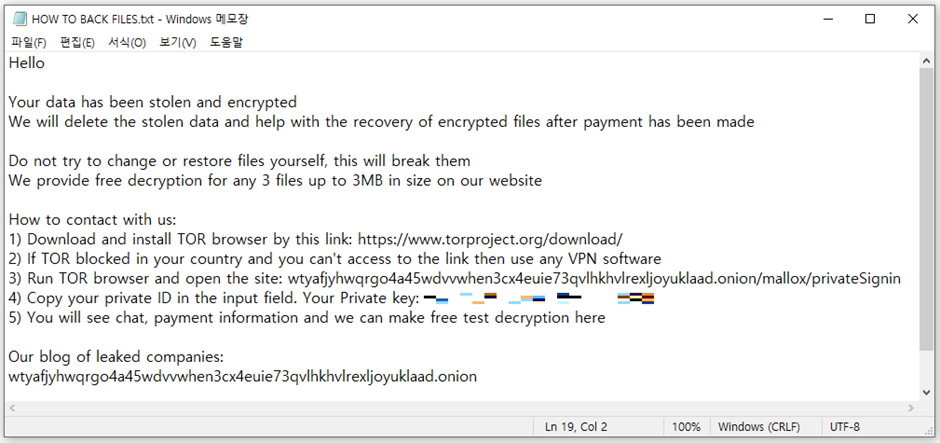
Mallox ransomware, known for targeting MS-SQL servers, was then installed to encrypt the system.
| Overview | Description |
| Encryption algorithm | AES-256 / SHA-256,AES-128-CTR [5] |
| Encryption extension | “.rmallox” |
| Ransom note filename | “HOW TO BACK FILES.txt” |
| Prioritized extensions for encryption | “.bak”, “.zip”, “.rar”, “.7z”, “.gz”, “.sql”, “.mdf”, “.hdd”, “.vhd”, “.vdi”, “.vmx”, “.vmdk”, “.nvram”, “.vmem”, “.vmsn”, “.vmsd”, “.vmss”, “.lck”, “.vhdx”, “.vhd”, “.dbf”, “.ora”, “.oraenv”, “.dmp”, “.ibd”, “.mdb”, “.smd”, “.mdb” |
| Paths excluded from encryption | “msocache”, “$windows.~ws”, “system volume information”, “intel”, “appdata”, “perflogs”, “programdata”, “google”, “application data”, “tor browser”, “boot”, “$windows.~bt”, “mozilla”, “boot”, “windows.old”, “Windows Microsoft.NET”, “WindowsPowerShell”, “Windows NT”, “Windows”, “Common Files”, “Microsoft Security Client”, “Internet Explorer”, “Reference”, “Assemblies”, “Windows Defender”, “Microsoft ASP.NET”, “Core Runtime”, “Package”, “Store”, “Microsoft Help Viewer”, “Microsoft MPI”, “Windows Kits”, “Microsoft.NET”, “Windows Mail”, “Microsoft Security Client”, “Package Store”, “Microsoft Analysis Services”, “Windows Portable Devices”, “Windows Photo Viewer”, “Windows Sidebar” |
| Files excluded from encryption | “desktop.ini”, “ntuser.dat”, “thumbs.db”, “iconcache.db”, “ntuser.ini”, “ntldr”, “bootfont.bin”, “ntuser.dat.log”, “bootsect.bak”, “boot.ini”, “autorun.inf”, “debugLog.txt”, “TargetInfo.txt” |
| Extensions excluded from encryption | “.msstyles”, “.icl”, “.idx”, “.avast”, “.rtp”, “.mallox”, “.sys”, “.nomedia”, “.dll”, “.hta”, “.cur”, “.lock”, “.cpl”, “.Globeimposter-Alpha865qqz”, “.ics”, “.hlp”, “.com”, “.spl”, “.msi”, “.key”, “.mpa”, “.rom”, “.drv”, “.bat”, “.386”, “.adv”, “.diangcab”, “.mod”, “.scr”, “.theme”, “.ocx”, “.prf”, “.cab”, “.diagcfg”, “.msu”, “.cmd”, “.ico”, “.msc”, “.ani”, “.icns”, “.diagpkg”, “.deskthemepack”, “.wpx”, “.msp”, “.bin”, “.themepack”, “.shs”, “.nls”, “.exe”, “.lnk”, “.ps1”, “.rmallox” |
| Terminated processes | Organized in Reference data |
| Terminated services | Organized in Reference data |
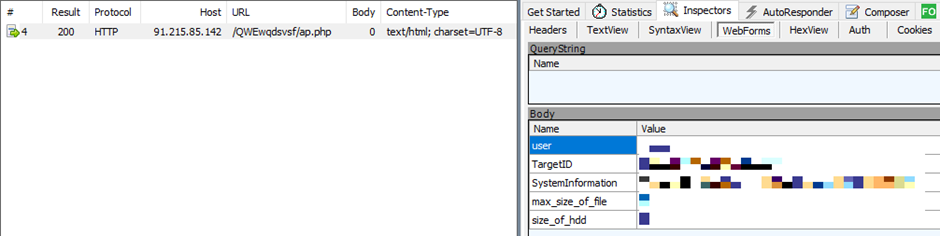
| C&C URL | hxxp://91.215.85[.]142/QWEwqdsvsf/ap.php |
| Others | Deletes volume shadow copies. Deactivates the termination feature. |
It uses a combination of AES-256 and SHA-256 encryption algorithms, appending a “.rmallox” extension to encrypted files.
Mallox has a function that lets it spread by getting into shared folders.
It also gets basic information from computers that are infected and sends it to the command and control site.
The ransomware meticulously avoids encrypting certain file paths and extensions, focusing on those with potentially valuable data.
Correlation with Previous Attacks
The attack patterns observed bear a striking resemblance to previous incidents involving the Tor2Mine CoinMiner and BlueSky ransomware.
The use of newly identified malware, targeting strategies, and the C&C server addresses suggest that these attacks are the work of the same threat group.
The continuous discovery of attacks by the TargetCompany group underscores the critical need for robust cybersecurity measures.
Administrators are urged to enforce strong password policies, regularly update their systems, and employ comprehensive security solutions to thwart such threats.
The persistence and sophistication of these attacks highlight the ongoing risk to MS-SQL servers and the broader digital ecosystem.
File and Behavior Detection
To assist in the detection and prevention of such attacks, cybersecurity entities have released identifiers for the malware used in these campaigns:
- Downloader/Win.Agent.C5614241
- Backdoor/Win.Remcos.C5607317
- Ransomware/Win.Mallox.C5601155
- Trojan/Win.Generic.C5352187
Behavior detection measures have also been updated to identify malicious activities associated with these attacks.
As the digital landscape continues to evolve, so too does the nature of cyber threats.
The recent campaign by the TargetCompany group serves as a stark reminder of the importance of vigilance and proactive security measures in safeguarding against ransomware attacks.
IoC
MD5
– 52819909e2a662210ab4307e0f5bf562: Remcos RAT (walkingrpc.bat)
– 20dd8410ff11915a0b1f4a5018c9c340: Remote screen control malware (launcher.exe)
– 09b17832fc76dcc50a4bf20bd1343bb8: Mallox ransomware (360. exe)
– 3297dc417cf85cfcea194f88a044aebd: Remote screen control malware – past case
– ff011e8a1d1858f529e8a4f591dc0f02: Remote screen control malware – past case
C&C Servers
– 80.66.75[.]238:3388: Remcos RAT
– hxxps://80.66.75[.]238:3030: Remote screen control malware
– hxxp://91.215.85[.]142/QWEwqdsvsf/ap.php: Mallox ransomware
– hxxps://5.188.86[.]237:3030: Remote screen control malware – past case
Download URL
– hxxp://42.193.223[.]169/extensioncompabilitynode.exe : Remcos RAT
Is Your Network Under Attack? - Read CISO’s Guide to Avoiding the Next Breach - Download Free Guide


