Researchers uncovered a new powerful Android malware called “Cookiethief ” that lunched by unknown cybercriminals to steal cookies from the browsers and Facebook app by acquiring the root access on the victim’s Android device.
Losing cookies to cybercriminals is deadly dangerous since web services use them to store on the device a unique session ID that can identify the user without a password and log in.
Stolen cookies let hackers obtain the session of the websites and use it to access the victim’s account on behalf of them for personal gain.
Cookiethief malware abusing the browser and Facebook app not because of the vulnerability, but malware could steal cookie files of any website from other apps and the same method used in the attack to steal the cookies.
Researchers believe that the Cookiethief malware possibly linked with widespread Trojans as Sivu, Triada, and Ztorg which all are a type of malware that exploits the OS vulnerabilities to get into the system folders.
A persistent backdoor like Bood, along with the auxiliary programs Cookiethief and Youzicheng, can end up on the device.
Cookiethief malware detects as “com.lob.roblox as HEUR:Trojan-Spy.AndroidOS.Cookiethief ., org.rabbit as HEUR:Trojan-Proxy.AndroidOS.Youzicheng, and Bood as HEUR:Backdoor.AndroidOS.Bood.a.
Cookiethief Infection Process
Initially, com.lob.roblox, a Package name of Cookiethief malware drop into the Android device that similar to that of the Roblox Android gaming client (com.roblox.client), but has nothing in common with Roblox.
Once it’s dropped, the malware connects to a backdoor installed on the same smartphone to execute the super command.
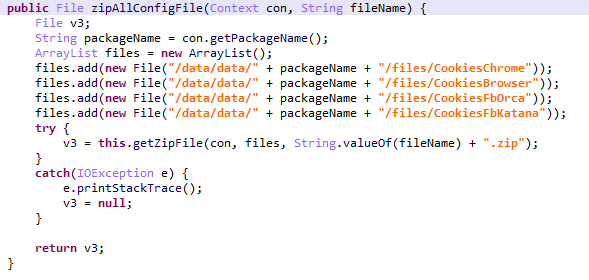
Later it passes a Shell command for execution as a result, a backdoor called Bood will be dropped into a path /system/bin/.bood that helps to launch a local server and executes commands received from Cookiethief.
Researchers found a C2 server that used in this attack has a part of the advertising services for distributing spam on social networks and messengers, which makes it harder to predict the motivation of this malware attack on Android users.
According to Kaspersky’s research ” However, during our analysis of Cookiethief, we uncovered another malicious app with a very similar coding style and the same C&C server. The second “product” from (presumably) the same developers (detected as: Trojan-Proxy.AndroidOS.Youzicheng) runs a proxy on the victim’s device.”
This malicious app is believed to be used to bypass the security system on the relevant messenger or social network using a proxy server on the victim’s device to avoid the detection and request to the website will look like a request from a legitimate account.
To implement this method, an executable file is first downloaded and run on the targeted device.
These two attacks used by the attackers to avoid raising suspicion from Facebook and the attacker is now in the initial stage.
Indicators of Compromise
MD5
65a92baefd41eb8c1a9df6c266992730
f84a43b008a25ba2ba1060b33daf14a5
c907d74ace51cec7cb53b0c8720063e1
c9c252362fd759742ea9766a769dbabe
8312e7c626cac368f0bd79c9c8da5bd7
Also Read: New Krampus-3PC Malware Attacks iPhone Users to Steal Cookies and Redirects to Malicious Websites



