Critical vulnerability in D-Link cloud camera allows attackers to hijack and intercept the camera to see the live video streaming and recorded videos.
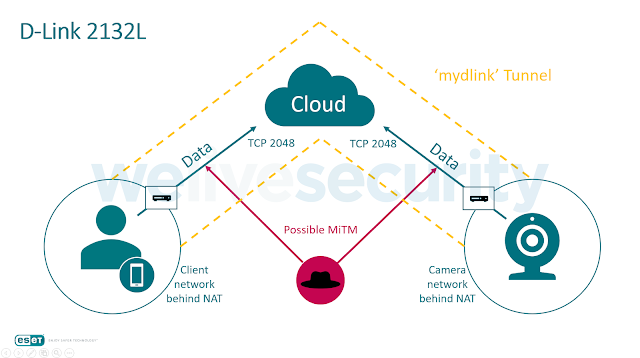
Researchers discovered that the D-Link camera communicate over unencrypted channel between the camera and the cloud and between the cloud and the client-side viewer app.
This flaw could allows an attacker to perform a Man-in-the-Middle attack and intercept the connection to spy on victims’ video streams.
The communication request between app and the camera establish over proxy server using a TCP tunnel where the only place the traffic is encrypted.
But some of the other sensitive content such as camera IP and MAC addresses, version information, video and audio streams, and extensive camera info are passing through the unencrypted tunnel.
The vulnerability resides in D-Link customized open source boa web server source code file called request.c is handling the HTTP request to the camera.

In this case, all the incoming HTTP request that handle by this file elevated to admin allow attacker to gain complete device access.
Another vulnerability discovered in the web browser plug-in called “mydlink services” that helps users to play the live playback via client web browser and it also manages the creation of the TCP tunnel where the plug-in forwarding requests for the video and audio data streams. refer the video demonstration blow,
According to ESET research, The tunnel is made available for the whole operating system, so any application or user on the client’s computer can simply access the camera’s web interface by a simple request (only during the live video streaming) to hxxp://127.0.0.1:RANDOM_PORT/.
“No authorization is needed since the HTTP requests to the camera’s web server are automatically elevated to admin level when accessing it from a localhost IP (viewer app’s localhost is tunneled to camera localhost).”
This vulnerability let hackers to replace the legitimate firmware with their own rigged or backdoored version.
Intercept the D-link Camera Video Streaming
An attacker who is sitting in the middle of the network traffic between the viewer app and the cloud or between the cloud and the camera, can see the HTTP requests for the video and audio packets using the data stream of the TCP connection on the server.
Later attackers can reply and reconstruct this captured packets at any time and the same way attacker obtain the current audio or video stream from that camera using following steps,
- Identify the traffic that represents video streams. This traffic consists of multiple blocks of data, each block having a specific header and defined length.
- Separate the data parts from the headers.
- Finally, the parts of the video are merged into one file.
Playing the video files obtained this way can be a little tricky as they are in a raw streaming format instead of a container file format. However, some media players can handle these raw formats if run with the appropriate command line switches ESET said.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity courses online to keep your self-updated.
Also Read:
ATM Skimming Attack – Scammers Hijack ATM’s built-in Security Camera to Steal User’s PIN



.png
)
