Firefox 66.0.4 released for both desktop and Android with the fixes for a recently discovered Firefox add-on bug let automatically disabled all the add-ons in the browser due to the expiration of the intermediary certificate.
In other words, we can say that Firefox forgot to handle certificate expiration for all add-ons, so all the legacy add-ons got disabled due not having a valid signature.
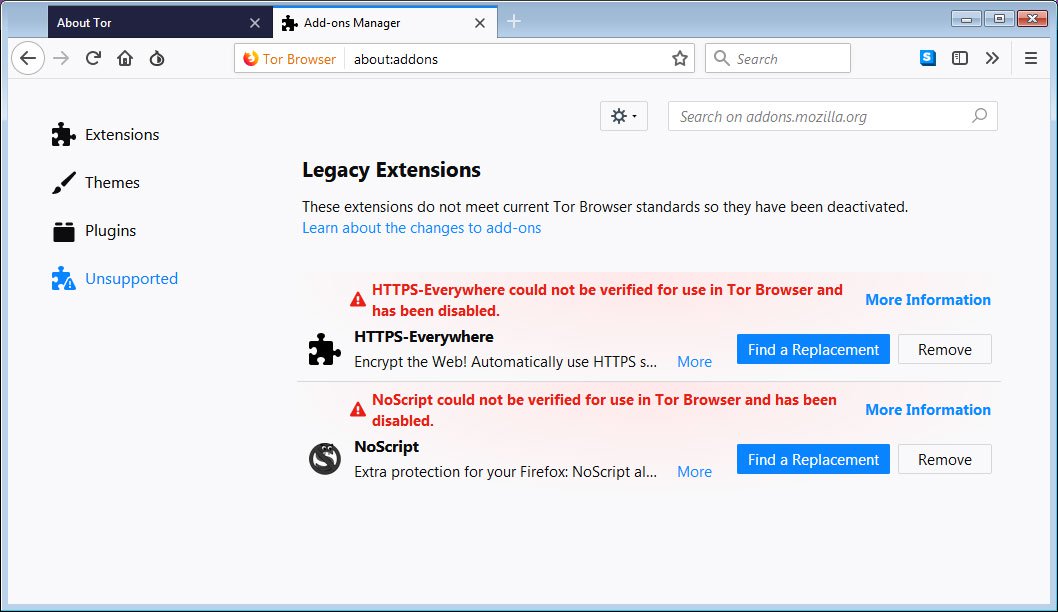
This impacts both Firefox and Tor, it also affects the important security add-ons NoScript and HTTPS-Everywhere which was disabled in Tor browser.
NoScript is an important security add-on that’s officially trusted by Tor, as well as being installed by millions of other regular browser users.
HTTPS Everywhere is a Firefox, Chrome, and Opera extension that encrypts your communications with many major websites, making your browsing more secure also it is one of the legacy extensions in Tor.
Even if the users were tried to reinstall the add-ons, it always failed to download the new add-ons and throw the error “failed to download”.
Users have faced the same issues in Firefox when users try to download the add-on installation that will be prevented by saying “the add-on downloaded from this site could not be installed because it appears to be corrupt”.

Since the Tor browser based on Firefox, all the addons should be signed with valid digital certification and the failed signature update caused this serious issue in both browsers.
you can disable this signature requirement by setting the xpinstall.signatures.required setting to false. valid signatures is a mandatory security feature, it should only be disabled until Tor releases a new version with a bundled fix.
about:config -> searchxpinstall.signatures.required, right-click on it, and select Toggle.
Firefox 66.0.4
This new release of Firefox 66.0.4 includes the fixes for the expired certificate and disabled add-ons.
Firefox team were continuously working for the past two days finally resolve the certificate chain to re-enable web extensions, themes, search engines, and language packs.
According to release note for Firefox 66.0.4 ” Repaired certificate chain to re-enable web extensions that had been disabled “

New version of Firefox 66.0.4 can be download here
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity courses online to keep your self-updated.


