Google released a new version of Chrome 103.0.5060.114, a stable chennal update with the fixes of security vulnerabilities, including a Zero-day bug that was exploited wide by unknown threat actors.
Chrome 103 was released with the fixed for 4 security vulnerabilities reported by external security researchers.
CVE-2022-2294, a Heap-based buffer overflow zero-day bug allows attackers to execute an arbitrary code remotely and bypass the protection mechanism, additionally, it leads to DoS: Crash, Exit, or Restart the affected system.
“A heap overflow condition is a buffer overflow, where the buffer that can be overwritten is allocated in the heap portion of memory, generally meaning that the buffer was allocated using a routine such as malloc()”. mitre explains.
Here are the other bugs that were fixed in this new security update:
- High CVE-2022-2294: Heap buffer overflow in WebRTC.
- High CVE-2022-2295: Type Confusion in V8. Reported by avaue and Buff3tts at S.S.L.
- High CVE-2022-2296: Use after free in Chrome OS Shell. Reported by Khalil Zhani
The Zero-day bug affected both Windows and Android versions and the bug was reported by Jan Vojtesek from the Avast Threat Intelligence team.
The attacker behind this exploit is still unknown. Google says this zero-day vulnerability was exploited in the wild and does not yet share technical details or any info regarding these incidents.
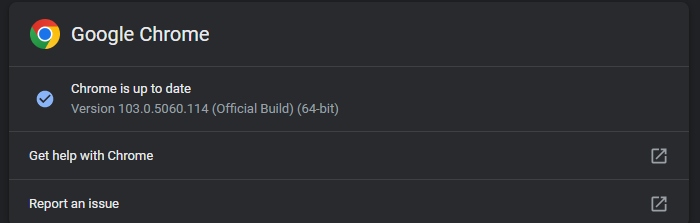
Chrome 103.0.5060.114 Update:
Users can update the new version of chrome by checking Chrome menu > Help > About Google Chrome, where it will check auto-update and request you to relaunch the browser after the patch gets downloaded.
As Google Confirms that the bug is active under attack, Users are urged to update chrome immediately to apply the patch.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates.



.png
)
