Researchers discovered a new firmware vulnerability in TP-link Archer C5 (v4) routers Let the attacker gain an Admin Password, and allow them remote takeover the router.
Once the vulnerability has successfully exploited, a remote attacker takes over the router configurated through Telnet on the local area network (LAN) and connects to a File Transfer Protocol (FTP) server via both LAN and WAN.
The vulnerability marked as “Critical” severity since it grants access to unauthorized third-party access due to the improper authentication, and it affects the TP-link Archer C5 router that deployed in both home and business environments.
It is very dangerous for business networks where router with this kind of critical vulnerability will allow an attacker to enable the Guest WiFi, through which an attacker enters into the internal network.
How Does the Router Vulnerability Can be Triggered by Attackers
An attacker could trigger the vulnerability by just sending the vulnerable HTTP request to be granted access to the device.
Basically, there are two types of requests that are considering here, one if “Safe” and another one if “Malicious”. In Safe requests, two parameters must be validated: TokenID and the JSESSIONID.
“But the Common Gateway Interface (CGI) validation here is only based on the referrer’s HTTP headers that used to matches the IP address or the domain associated with tplinkwifi.net, and then the routers Main domain (HTTPD), will recognize it as valid .”
In this case, The vulnerability affected both HTTP POST and GET requests and voiding the admin password when string length exceeds the allowed number of bytes.
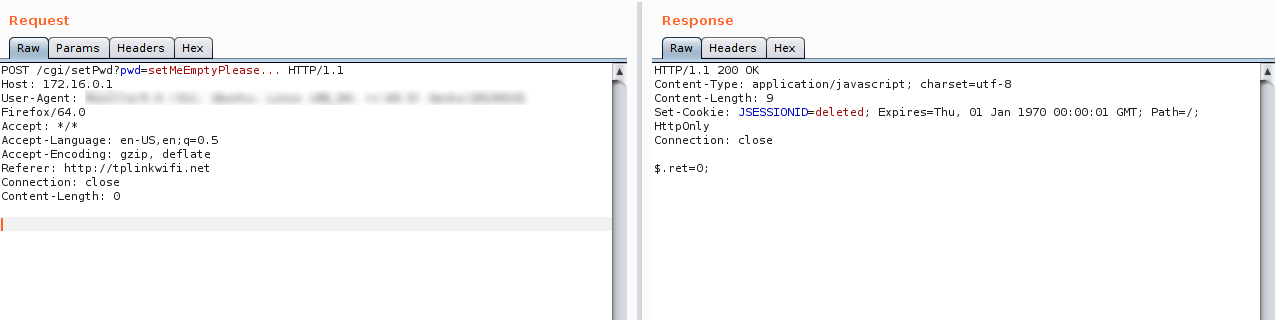
According to IBM report , “The short way of describing this flaw is vulnerable HTTP requests that void the user’s password. In an overflow issue of sorts, when a string that’s shorter than the expected string length is sent through as the user’s password, the password value gets distorted into some non-ASCII bytes.”
The vulnerability has been reported to the TP-link and the patch has been issued on version TP-Link Archer C5 v4 and other versions that may be exposed.
You can also read the complete firmware analysis to know more about this vulnerability and how it was discovered.



