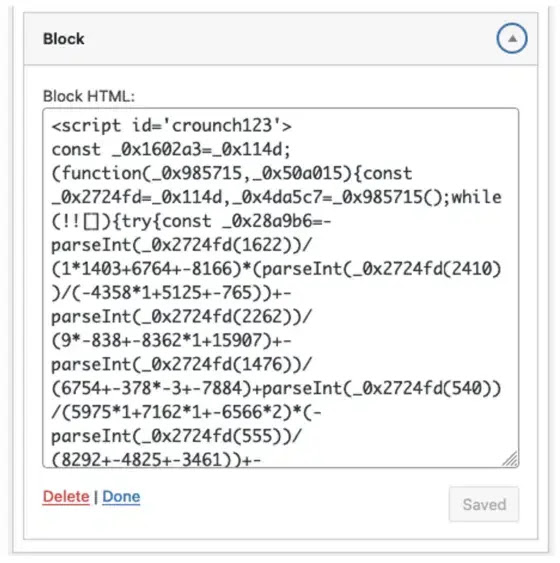
Researchers analyzed a new stealthy credit card skimmer that targets WordPress checkout pages by injecting malicious JavaScript into the WordPress database.
On checkout pages, the malware is designed to steal credit card information from users who are visiting those pages.
Whenever the page for the checkout is loaded, the malware examines the URL for the word “checkout” to make certain that it is functioning properly on the appropriate page.

Once the malware has been activated, it will inject a fake payment form that is designed to look like a legitimate payment processor. As the user fills out the fields on the form, the form is designed to record the credit card information that they provide.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free
Malware can also take over pre-existing payment fields on a page in order to steal information from those fields. Through the utilization of Base64 encoding and AES-CBC encryption, it conceals the data that has been stolen.
It is then possible to exfiltrate the stolen data from the victim’s website by utilizing the navigator.sendBeacon function, which enables the data to be transmitted in a background manner without being detected.
A visitor’s sensitive payment information can be stolen by malware, which can then be used for fraudulent transactions or sold on underground markets, making the malware a dangerous threat.
According to Sucuri Blog, users examine their own Custom HTML widgets in search of script tags that are unfamiliar or suspicious in order to identify malicious software.
Users can also lessen the impact of this threat by ensuring that their WordPress sites are up-to-date and that they have the most recent security patches installed.
Two-factor authentication and regular reviews of all admin accounts are also recommended as preventative measures, while the owners of websites have the ability to implement file integrity monitoring in order to identify any unauthorized changes made to the files of their websites.
The use of a website firewall also allows for the blocking of malicious traffic and the prevention of attempts to hack the server from reaching the platform.
Find this News Interesting! Follow us on Google News, LinkedIn, and X to Get Instant Updates!



.png
)
