Researchers discovered a new malware variant dubbed Gafgyt infect IoT devices specifically routers used in a small office and home network. The malware variant targets commercial routers like Zyxel, Huawei, and Realtek.
It exploits remote execution code vulnerability in routers to gain access and recruit them to into botnets to attack gaming servers.
Vulnerability Exploited
According to Unit 42 researchers, there are more than 32,000 WiFi routers are vulnerable to the exploits. It abuses the following vulnerabilities to gain access to the routers.
- CVE-2017-18368 – ZYXEL P660HN-T1A – New in this variant
- CVE-2017-17215 – Huawei HG532 – Present in JenX as well.
- CVE-2014-8361 – Realtek RTL81XX Chipset – Present in JenX as well.
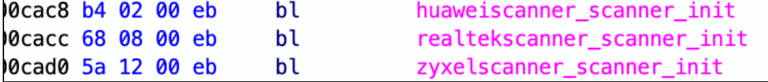
The Gafgyt malware active since 2014, it is known for conducting large-scale DDoS attack, the malware includes three scanners that exploit the remote code execution vulnerabilities present on the routers.
The exploits crafted as binary droppers, which downloads the binary from the malicious server based on the router type and try to infect them.
CVE-2017-18368 – ZYXEL P660HN-T1A
The first exploit is a command injection on Zyxel P660HN wireless routers, the command injection vulnerability resides in [ViewLog.asp] page and it can be exploited through the remote_host parameter.
CVE-2017-17215 – Huawei HG532
The second exploit abuses a remote code execution vulnerability found on HG532 routers. the vulnerability can be exploited by an attacker sending malicious packets to TCP port 37215 to launch attacks.
CVE-2014-8361 – Realtek RTL81XX Chipset
The flaw disclosed in 2014 with some Realtek routers which lead to remote code execution.”The miniigd SOAP service, implemented in Realtek SDK, allows remote attackers to execute arbitrary code via a crafted NewInternalClient request,” reads blog post.
The Gafgyt malware variant uses different attack types based on the commands received from the C2 server. Following are the commands
HTTP – HTTP flooding attack
HTTPHex – Aimed to exhaust server resources
HTTPCF – Attack against services secured by Cloudflare
KILLER & KILLATTK – Kills competing botnets
VSE – Payload to attack gaming servers
The gaming servers are the primary target, “payload is widely used to cause a Distributed Reflection Denial of Service (DrDoS), which involves multiple victim machines that unwittingly participate in a DDoS attack.”
Unit 42 observed that the botnets are advertised on social media such as Facebook and Instagram, and the attackers also have their websites to rent the botnets.
The malware samples and DOS attacks are easily obtained by anyone online by just spending a few dollars.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



