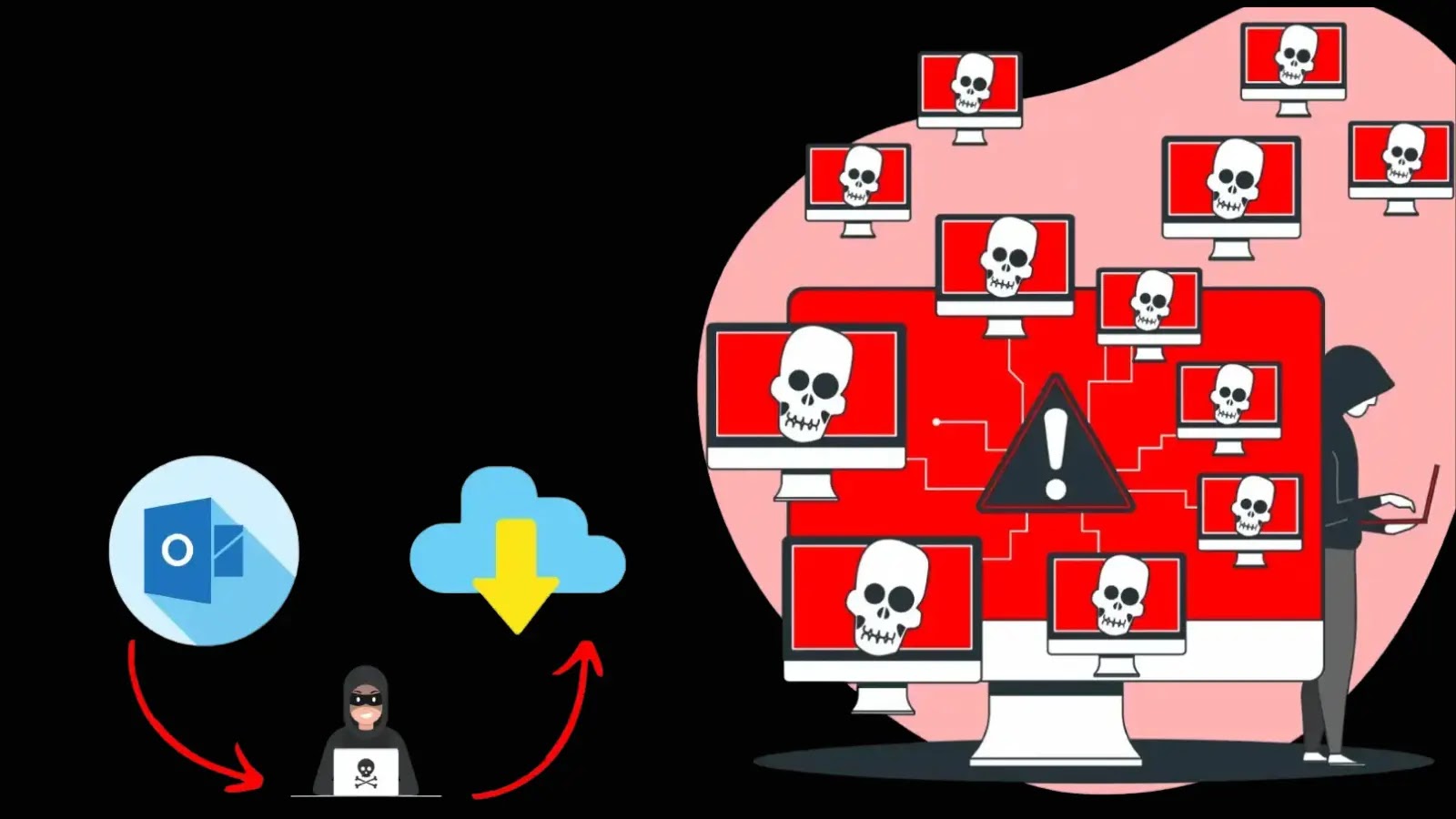
Recently, it’s been confirmed by Microsoft that the current outage problems experienced by the following services of Microsoft were due to intentional Layer 7 DDoS attacks:-
- Azure
- Outlook
- OneDrive
The credit for the attacks goes to a threat actor called Storm-1359 (aka Anonymous Sudan), as per Microsoft’s findings.
Microsoft observed a rise in web traffic targeting specific services starting in early June 2023, resulting in temporary availability issues.
Without any delay, Microsoft instantly started monitoring the ongoing DDoS attacks thoroughly by launching a quick investigation.
Layer 7 DDoS Attacks
Rather than targeting layer 3 or layer 4, the recent DDoS attacks have primarily targeted layer 7.

To enhance customer protection against similar DDoS attacks, Microsoft strengthened layer 7 defenses by optimizing Azure Web Application Firewall (WAF).
Microsoft discovered that Storm-1359 could use different cloud services and open proxies to launch DDoS attacks using several botnets and tools.
Moreover, here below, we have mentioned the main focuses of Storm-1359:-
- Causing disruptions
- Attracting public attention
In a report published recently, Microsoft provided an introductory analysis of the root cause, suggesting DDoS attacks as the potential reason behind the Azure outage, highlighting a noticeable surge in network traffic.
In a Layer 7 DDoS attack, threat actors specifically direct their efforts towards the application level, aiming to overload services by flooding them with excessive requests.
This huge flood of requests overwhelms the services, causing them to become unresponsive since they cannot handle the load.
The threat actors employ multiple DDoS methods to overpower a web service, exhausting its connection pool and causing it to accept new requests.
Types of DDoS Attack Traffic
Here below, we have mentioned all the types of layer 7 DDoS attack traffic:-
- HTTP(S) flood attack
- Cache bypass
- Slowloris
Recommendations
Here below, we have mentioned all the recommendations offered by Microsoft:-
- To protect web apps, make sure to use layer 7 protection services like Azure Web Application Firewall (WAF).
- Stay protected against known bad bots by implementing the bot protection managed rule set.
- Make sure to block the IP addresses and ranges that you identify as malicious.
- Unknown and suspicious traffic should be blocked.
- To block and limit the HTTP or HTTPS attacks automatically that have known signatures, create custom WAF rules.
Looking For an All-in-One Multi-OS Patch Management Platform – Try Patch Manager Plus