A vulnerability in Microsoft Power BI allows unauthorized users to access sensitive data underlying reports, which affects tens of thousands of organizations and grants access to employee, customer, and potentially confidential data.
By exploiting this vulnerability, attackers can extract information beyond what is visible in the reports, including additional data attributes, records, and details behind aggregated or anonymized data.
The vulnerability was reported to Microsoft by Nokod Security, but they consider it a feature rather than a security issue, while Power BI semantic models expose all underlying data, including hidden tables, columns, and detailed records, even when only aggregated data or a subset of the data is visualized in the report.
It grants unintended access to sensitive information for any user with access to the report, regardless of sharing permissions or filtering applied in the report view, which applies to both internal and publicly shared reports.
Details Of Exploitation:
Public Power BI reports trigger data retrieval upon execution through a POST request to the “/public/reports/querydata” endpoint on the wabi-west-europe-f-primary-api.analysis.windows.net server.
In contrast, organizational reports leverage a different endpoint on pbipweu14-westeurope.pbidedicated.windows.net, specifically “/webapi/capacities/<capacityObjectId>/workloads/QES/QueryExecutionService/automatic/public/query”, which likely relies on a capacity object identifier for authorization.
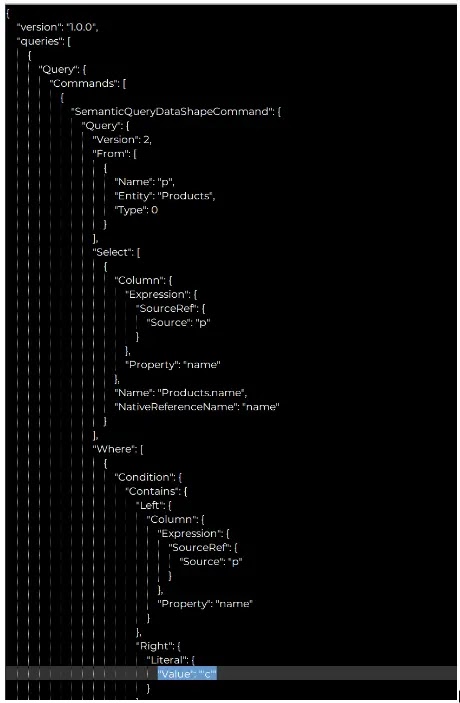
It triggers individual API calls with JSON payloads specifying queries in a proprietary format, by targeting data in the report’s underlying semantic model, where users can request data from both visible and hidden columns/tables, as long as they’re part of the model.
The first example demonstrates retrieving the “name” column from the “Products” table and filtering for products containing the letter “c,” highlighting how each visual effectively executes a custom query to fetch its specific data requirements.
.webp)
An attacker can exploit Power BI reports to access hidden data. While removing filters and aggregations in visualizations is simple, adding unseen data requires knowledge of the data schema.
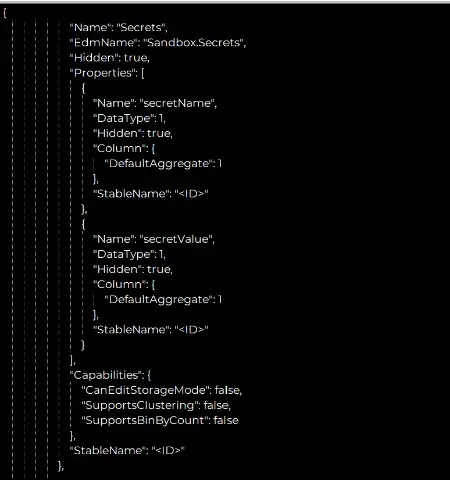
This schema can be retrieved from a public report’s “/conceptualschema” endpoint or an organizational report’s “/explore/conceptualschema” endpoint, which exposes the entire semantic model, including hidden columns and tables, even if the report creator marked them as hidden, which empowers the attacker to craft further requests to access the hidden information.
A vulnerability exists where a SQL table hidden within a Power BI report can still be accessed through the “query” API even though it’s not returned by the “conceptualschema” API.
.webp)
According to Nokod Security, the vulnerability is particularly concerning for organizations that share reports containing confidential information like financial data or healthcare records.
Finding dozens of reports that could be used against people from different groups, like universities and government websites, showed that the underlying data model can be accessed through API calls and can reveal private data like PII and PHI.







.webp)
.webp)

.webp)