Dell Technologies recently disclosed a data breach involving a company portal that contained limited customer information related to purchases.
The breach exposed customer names, physical addresses, and detailed order information, including service tags, item descriptions, order dates, and warranty details.
However, Dell has confirmed that no financial data, email addresses, phone numbers, or other highly sensitive information were accessed during the incident.

Upon discovering the breach, Dell promptly initiated security response procedures, began an investigation to assess its extent, and took steps to contain it.
Free Webinar on Live API Attack Simulation: Book Your Seat | Start protecting your APIs from hackers
The company also notified law enforcement authorities and engaged a third-party forensics firm to investigate the incident further.
Dell has emphasized that, given the nature of the data involved, there is no significant risk to customers from this breach.
However, they advise customers to remain vigilant against potential tech support scams and to report any suspicious activity related to their Dell accounts or purchases to [email protected].
Information on the Dark Web
In a related development, a threat actor claimed to be selling a massive database on a hacking forum, allegedly containing nearly 49 million records from Dell.
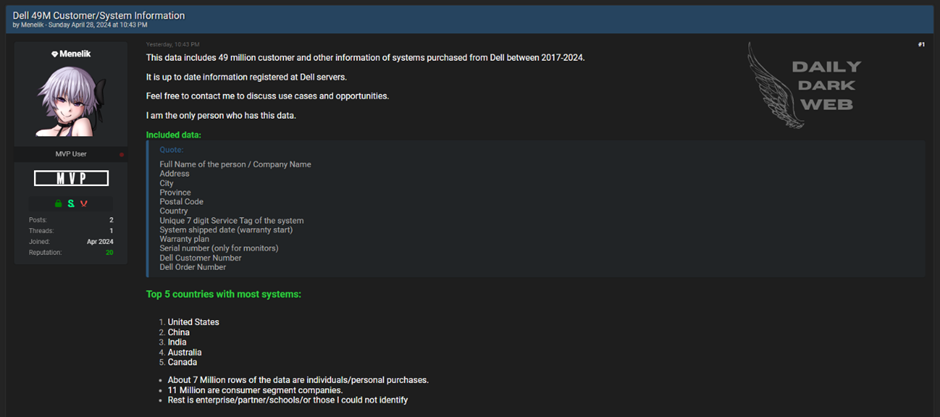
This database reportedly includes
- Customer names, email addresses, hashed passwords
- Dell product details like serial numbers and purchase orders
- Employee records
While financial information and payment details were not included in this dataset, exposing such extensive customer and employee information could potentially facilitate phishing, scams, and identity theft targeting Dell’s customer base.
Cybersecurity experts caution that even non-financial data, such as names, email addresses, and purchase histories, can be exploited through social engineering attacks, credential stuffing, and other malicious activities.
Data breaches, even those not involving direct financial loss, can still lead to significant consequences for the affected individuals and the company, including reputational damage and loss of trust.
Dell continues investigating the breach and has enhanced security measures to prevent future incidents.
Customers are encouraged to monitor their accounts for any unusual activity and to take precautions to protect their personal information.
Is Your Network Under Attack? - Read CISO’s Guide to Avoiding the Next Breach - Download Free Guide



.webp)





.webp)
.png)