The latest Nexusguard DDoS Trend Report for 2024 has unveiled a significant escalation in the size of Distributed Denial of Service (DDoS) attacks throughout 2023, with an average increase of 233.33% compared to the previous year.
Despite a 54.74% drop in the total number of attacks, the dramatic rise in attack size indicates a strategic shift towards more potent and disruptive cyber assaults.
In 2023, the digital landscape witnessed a transformative wave of DDoS attacks, challenging the conventional understanding of cyber threats.
Industries ranging from gaming to financial services were targeted in these attacks, underscoring the pervasive risk of DDoS across sectors.
Notably, the most significant attack recorded peaked at an unprecedented 700 Gbps, marking a 93.42% increase from the year before.
Hacktivism emerged as a key motivator behind these attacks, with political agendas driving the targeting of government and vital services.
This politicization of cyber tactics highlights the growing intersection between cybersecurity and national security concerns.
Free Webinar on Live API Attack Simulation: Book Your Seat | Start protecting your APIs from hackers
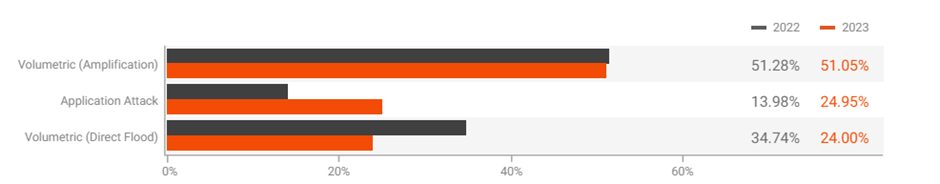
The Prevalence of UDP-based Attacks
Despite the overall decrease in attack frequency, UDP-based attacks remained the most predominant type in 2023, although they saw a 58.29% year-on-year decrease.
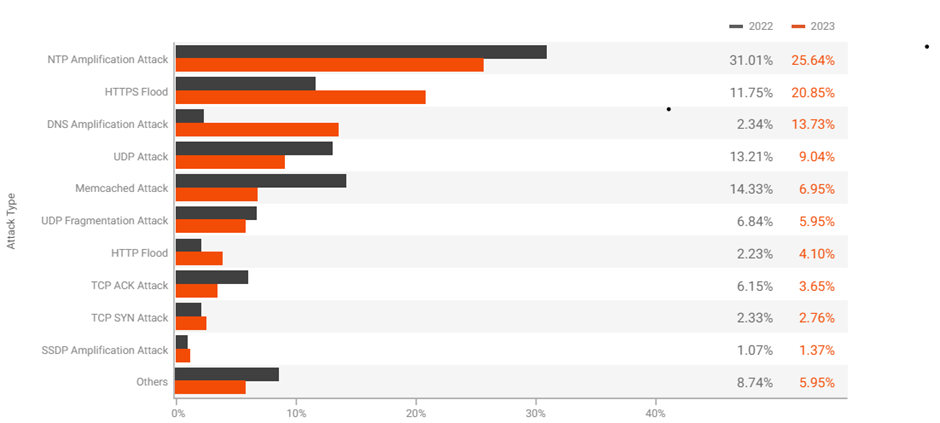
The persistence of UDP-based attacks can be attributed to their simplicity and effectiveness in overwhelming target networks with a flood of packets, making them a favored choice among attackers.
The Nexusguard report’s findings suggest a strategic shift among cybercriminals towards executing fewer but more devastating attacks.
This is evidenced by the significant rise in the average size of DDoS attacks, which suggests attackers opt for quality over quantity.
The focus on larger-scale assaults is likely aimed at maximizing disruption and achieving a more significant impact with each attack.
The Role of Multi-Vector Attack Combinations
The analysis also highlighted the role of multi-vector attack combinations, which leverage multiple attack vectors simultaneously, making them harder to defend against.
The top three multi-vector attack vectors identified were HTTP Flood and HTTPS Flood, DNS Amplification and UDP Fragmentation, and TCP ACK and UDP Attack.
These combinations underscore the evolving sophistication of DDoS attacks and the need for equally advanced defense mechanisms.
The analysis reveals that Pakistan, Brazil, Libya, and the United States are the top countries targeted by Reflected DDoS attacks in 2023.
Specifically, Pakistan leads with a significant margin, followed by Brazil, Libya, and the United States.
Mitigation and Preparedness Strategies
The report emphasizes the importance of enhanced preparedness against sophisticated DDoS attacks.
Organizations are urged to invest in real-time threat intelligence, robust infrastructure resilience, and collaborative defense mechanisms.
Public awareness and education, alongside comprehensive policy and regulatory frameworks, are critical components in combating the evolving threat landscape.
The Nexusguard DDoS Trend Report for 2024 paints a concerning picture of the current state of cyber threats, with a notable increase in the size of DDoS attacks despite a decrease in their overall frequency.
The persistence of UDP-based attacks and the emergence of complex multi-vector attack combinations call for a dynamic and adaptive approach to cybersecurity defenses.
As the digital landscape continues to evolve, so must the strategies employed to protect against these disruptive and potentially devastating attacks.
Is Your Network Under Attack? - Read CISO’s Guide to Avoiding the Next Breach - Download Free Guide



%20(1).webp)





.webp)
.png)