A critical vulnerability has been discovered in XZ Utils, a widely used data compression tool across Unix-like operating systems, including Linux.
This vulnerability, identified as CVE-2024-3094, involves a backdoor that could potentially allow unauthorized remote access, posing a significant threat to software supply chain security.
The Discovery of CVE-2024-3094
The initial alarm was raised by Andres Freund, who noticed unusual activity in the XZ Utils project. Versions 5.6.0 and 5.6.1 of XZ Utils were found to be compromised.
Shortly after Freund’s warning, the United States government’s Cybersecurity and Infrastructure Security Agency (CISA) and the Open Source Security Foundation (OpenSSF) issued alerts about the critical nature of this backdoor, emphasizing the urgency of addressing this vulnerability due to its potential impact on OpenSSH security.
AI-Powered Protection for Business Email Security
Trustifi’s Advanced threat protection prevents the widest spectrum of sophisticated attacks before they reach a user’s mailbox. Try Trustifi Free Threat Scan with Sophisticated AI-Powered Email Protection .
The revelation of this backdoor is particularly alarming because it represents a nightmare scenario for software supply chain security.
XZ Utils is integral to embedded systems and firmware development across various ecosystems, with the Linux ecosystem being a primary target due to its role in powering modern cloud infrastructure.
The Response and Mitigation Efforts
In response to the discovery of CVE-2024-3094, the community acted swiftly.
This xz-utils Backdoor Found in Kali Linux Installations – Check for Malware Infection
Many Linux distributions impacted by the vulnerability have rolled back to a known safe version of XZ Utils, demonstrating the effectiveness of industry-wide, community-driven coordination.
However, the challenge remains in quickly detecting and deactivating deployed backdoored versions in the field.
Traditional detection tools, which often rely on simple version checks, hash-based detection, or YARA rules, have proven inadequate.
These methods can lead to alert fatigue and false positives, overwhelming security teams.
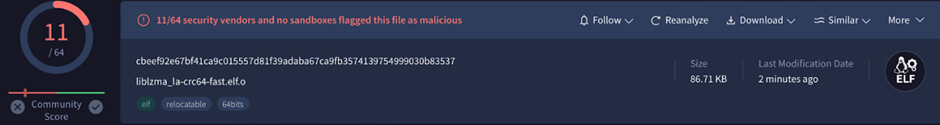
Recognizing the limitations of existing detection methods, the Binary Research Team developed a tool to identify the backdoored binaries.

Their investigation revealed the complexity of the XZ Utils backdoor, believed to be part of a sophisticated, state-sponsored operation with multi-year planning.
An essential technique employed by the backdoor involves the GNU Indirect Function (ifunc) attribute, which allows for runtime resolution of indirect function calls.
The backdoor intercepts execution and modifies ifunc calls to insert malicious code.

This static analysis method can generically detect tampering of control flow graph transitions, significantly reducing the false positive rate.
The discovery of the XZ Utils backdoor underscores the critical importance of software supply chain security.
Through the collaborative efforts of the security community and the innovative solutions provided by teams like Binary, the industry is better equipped to defend against these sophisticated threats.
As the landscape of cyber threats continues to evolve, such proactive measures and tools will be indispensable in safeguarding our digital infrastructure.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.



.webp)






